Securing Your Success
Expert Security Technology Solutions










Who We Are
Priveon provides Network Security Solutions and Expert Training by combining the best engineering talent, innovative solutions, and leading hardware and software vendors to produce results that make our customers successful. Ensure your success by engaging directly with Priveon on your company’s advanced security projects, or through the many partnerships who leverage Priveon’s proven and trusted services and training delivery practices.
Our Commitment
Our Commitment to our customers is to provide proven best practices and highly experienced engineers with every engagement. Our success is defined by your success.
Our Philosophy
Our Philosophy is to include knowledge transfer with every services engagement – enabling & empowering our customers and ensuring project success.
Priveon’s experts have become Masters in their Craft. We share this experience directly with our customers through project engagements, training content creation and delivery, online communication, research and publications.
Priveon Engineers are Experts in Cisco Advanced Security Products and Solutions
Let our experienced consultants and engineers provide proven design and delivery services to ensure project success. Priveon also partners with Cisco and their extensive partner community to deliver expert services and training to their customers. This includes Proof-of-Value delivery, implementation/integration services, post-sales support contracts, API and 3rd party integrations, as well as a number of other enablement services.
Network Security
- Firepower
- ASA
- Meraki
Visibility & Enforcement
- Identity Services Engine (ISE)
- Stealthwatch
- Software Defined Access (SDA)
Advanced Threat
- AMP For EndPoints
- Threat Grid
Cloud, Web & Email Security
- Umbrella DNS Security
- Cloudlock
- Web Security (WSA)
- Email Security (ESA)

Priveon Solution Highlight
Cisco Identity Services Engine (ISE)
READ MORE
Cisco Identity Services Engine (ISE) provides much more than Network Access Control.
Our Subject Matter Experts (SMEs) have successfully deployed and integrated ISE for use cases across wired, wireless and VPN access, including:
- Guest Lifecyle Management
- BYOD
- Wired and Wireless 802.1X
- Profiling
- Posture and Compliance
- Device Administration
- MDM integration
- Solution integration with pxGrid
- Cisco ACS migrations
Our ISE experts are trained across Security, Access, Route/Switch and Data Center technologies to ensure successful integration.
Priveon customized ISE services:
- Design and Deployment
- Implementation services from High Level Design to knowledge transfer and documentation
- Consulting Services
- Review existing installations and provide advice and guidance
- Provide recommendations to improve network security, optimize operations and maximize the value of your ISE investment
- Upgrades and Migrations
- NAC and ACS to ISE
- ISE software and hardware upgrades
- Heath Checks
- Fixed and customized assessments
- Health status analysis and best practice adherence
- Training
- Customized to your needs
Did You Know?
Priveon is a Non-Competitive Partner-first organization.Our unique “services-first” business model allows us to partner with manufacturers and their Partner communities rather than directly compete. Partner with us to take your team to the next level with Priveon expert services and training delivery.
How We Work With You:
Direct to Customer
Priveon supports its direct customer base with a proven solution delivery practice and expert consulting engagements. Let our experienced consultants and engineers provide proven delivery services to ensure project success. We include operational knowledge transfer with every engagement to strengthen your team’s knowledge base. As your Trusted Advisor, your success means our success.
Partners & Resellers
Partner with Priveon to enhance your company’s services delivery team. Whether it’s overflow projects where you need additional resources to meet customer deadlines, or it’s a technology/solution skill-set we can add to you delivery team, Priveon can assist and partner with you to ensure customer success.
- Pre-project scoping
- Product Specifications and Bill of Materials (BoM) Creation
- Project/Solution Delivery and Consulting Services
- Training and Knowledge Transfer
Product Manufacturers
Priveon has strategic partnerships with the solution vendors and product manufactures we support. Our consultants engage directly with the product business units and Field/Partner enablement teams.
- Formal Training – Content and Lab creation
- Training Delivery – Onsite or Remote
- Partner Development
- Service Delivery – Let us augment your existing service delivery team
- Field product/solution Feedback – Product Enhancements
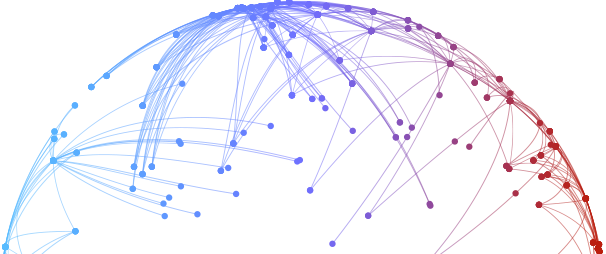
Countries
U.S. States
Red Balloons
Priveon Global Impact
| Title | Address | Description |
|---|---|---|
Mexico | Mexico | |
United States | United States | |
Ecuador | Ecuador | |
Seoul | Seoul, South Korea | |
Thailand | Thailand | |
Sydney | Sydney NSW, Australia | |
Melbourne | Melbourne VIC, Australia | |
Denmark | Denmark | |
Austria | Austria | |
Saudi Arabia | Saudi Arabia | |
Spain | Spain | |
Berlin | Berlin, Germany | |
Helsinki | Helsinki, Finland | |
Prague | Prague, Czechia | |
London | London, UK | |
Toronto | Toronto, ON, Canada | |
Vancouver | Vancouver, BC, Canada | |
Montreal | Montreal, QC, Canada | |
Amsterdam | Amsterdam, Netherlands | |
Frankfurt | Frankfurt, Germany | |
Paris | Paris, France | |
Jakarta | Jakarta, Indonesia | |
Singapore | Singapore | |
Dubai | Dubai - United Arab Emirates |
Would You Like to Know More?
Send us your info to schedule a call with a Priveon Consultant
Priveon, Inc.
Securing Your Success - Expert Security Technology Solutions
Copyright © 2023 Priveon, Inc. All Rights Reserved
MEET PRIVEON
